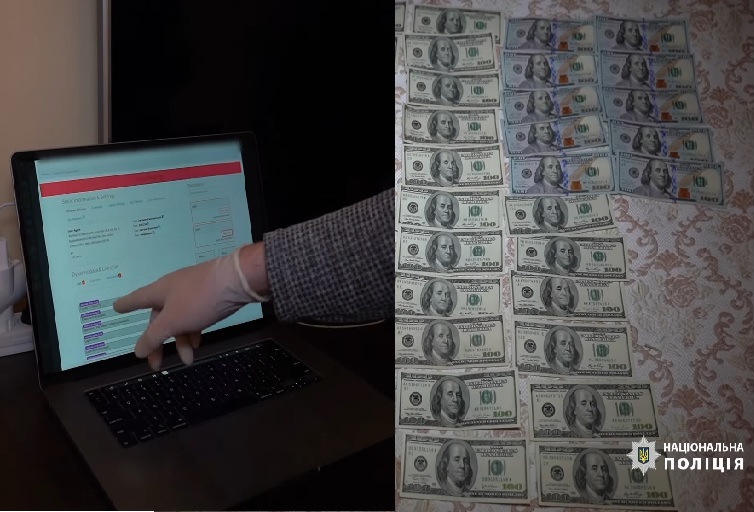
The Ukrainian authorities shut down one of the largest phishing services. The operation also involved authorities in the U.S. and Australia.
According to them, this was one of the largest such services in the world. Hackers used it in attacks against financial institutions in 11 countries. Thus, they managed to steal tens of millions of dollars.
Phishing as a service
According to the attorney’s general office in Ukraine, the authorities managed to identify a 39-year-old man. He develope a phishing package as a service and also a an administrative panel for it.
Afterwards, they were aiming several banks in Australia, Europe and the U.S. During the operation, police workers confiscated computers, mobile phones and hard drives.
According to Brian Krebs, security researcher, the operation has to do with the U-Admin phishing framework. So, the framework used fake web pages, in order to obtain victims’ credentials.
According to the authorities, villains used the toolkit in more than 50% of the phishing attacks in Australia, during 2019.
Technical support for “customers”
According to the attorney, the attacker sold its products on the dark web. But an unusual detail is that he presumably provided technical support during the attacks.
The officials mentioned they identified more than 200 buyers of the malicious software.
U-Admin allowed hackers’ customers to inject malicious code into victims’ browsers and steal their data on compromised websites. The hacker developed a sophisticated system, so that it could also capture two-factor authentication codes.
The hacker was arrested and it faces charges for creating and distributing malicious software. Also, the prosecutors accuse him of braking into computer networks. Thus, he may face up to six years in prison, for these charges.
A few days ago, the Ukrainian authorities managed to shut down the “world’s most dangerous malware.” The Emotet malware infected people’s computers by email. The messages included malicious download links, document macros and PDFs.